Ledger vs Hot Wallets: Security Architecture Analysis
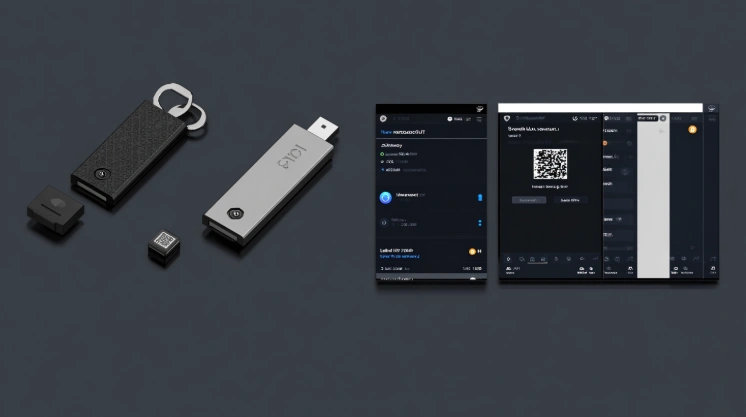
Ledger vs hot wallets comparison examines fundamental hardware vs software wallet security architecture differences affecting cold storage vs hot storage selection for crypto wallet safety comparison purposes.

Ledger vs hot wallets comparison examines fundamental hardware vs software wallet security architecture differences affecting cold storage vs hot storage selection for crypto wallet safety comparison purposes. The security analysis covers protection mechanisms, vulnerability profiles, and attack resistance across private keys storage methodologies. Understanding security architecture enables appropriate wallet selection for crypto security requirements.
Security comparison addresses architectural differences between offline and online storage solutions affecting long-term protection. Each approach offers distinct advantages requiring evaluation against specific use cases. This documentation covers security analysis methodology for Ledger versus hot wallet evaluation.
This security overview covers security features, recovery options, asset protection, and attack scenarios for hardware wallet versus software wallet assessment via USB-C or Bluetooth devices across all supported coins.
Security Features
Security Features for Ledger vs hot wallets examine hardware vs software wallet protection through cold storage vs hot storage architecture including offline storage ledger methodology, internet-connected wallets vulnerability assessment, and phishing & malware protection capabilities for crypto wallet safety comparison context. The features address private keys isolation effectiveness. Security ensures cold storage protection evaluation for hardware wallet users.
Security architecture fundamentally differs between storage methodologies for hardware wallet users.
Offline Storage Ledger
Offline storage ledger air-gapped protection:
| Security Element | Ledger | Hot Wallet |
|---|---|---|
| Key location | Offline secure element | Online device |
| Network exposure | Zero | Continuous |
| Remote access | Impossible | Potential target |
| Signing location | On device only | Internet-connected |
| Physical requirement | Device present | Network access |
Offline storage ledger establishes Ledger vs hot wallets core security difference. The hardware vs software wallet offline ensures cold storage vs hot storage via USB-C across all supported coins.
Internet-Connected Wallets Vulnerability
Internet-connected wallets vulnerability online exposure:
- Constant network connection maintained
- Remote attack vector availability
- Browser extension vulnerabilities
- Mobile app exploit potential
- Server-side compromise risk
- API attack surface exposure
- DNS hijacking susceptibility
Internet-connected wallets vulnerability presents crypto wallet safety comparison online risks. The cold storage vs hot storage online supports hardware wallet via USB-C or Bluetooth unlike software Trezor or KeepKey hot wallet alternatives across all supported coins.
Phishing and Malware Protection
Phishing & malware protection threat resistance:
| Protection comparison |
|---|
| Ledger: Transaction verified on device — Hot wallet: Displayed on computer/phone |
| Ledger: Address confirmed physically — Hot wallet: Software display only |
| Ledger: Keylogger immune — Hot wallet: Keylogger vulnerable |
| Ledger: Clipboard hijack protection — Hot wallet: Clipboard vulnerable |
| Ledger: Screen overlay immune — Hot wallet: Overlay attack possible |
Phishing & malware protection completes Ledger vs hot wallets threat analysis. The hardware vs software wallet protection ensures private keys via USB-C.
Recovery and Backup
Recovery and Backup for Ledger vs hot wallets examine hardware vs software wallet continuity through cold storage vs hot storage backup methodology including seed phrase protection approaches, backup methods hot wallet procedures, and self-custody ledger advantage assessment for crypto wallet safety comparison recovery context. The backup addresses private keys disaster recovery. Recovery ensures cold storage continuity for hardware wallet users.
Backup methodology affects disaster recovery for hardware wallet users.
Seed Phrase Protection
| Protection Aspect | Ledger | Hot Wallet |
|---|---|---|
| Generation | On device offline | On device/server |
| Storage | User controlled | User controlled |
| Exposure risk | Never online | May be online |
| Recovery location | Physical device | Software interface |
| Verification | Recovery Check app | Variable methods |
Seed phrase protection establishes Ledger vs hot wallets backup security. The hardware vs software wallet seed ensures cold storage vs hot storage via USB-C across all supported coins.
Backup Methods Hot Wallet
- Seed phrase written down
- Cloud backup options (risky)
- Password manager storage
- Encrypted file backup
- Social recovery methods
- Multi-device sync backup
Self-Custody Ledger Advantage
Self-custody comparison: Ledger offers complete key ownership, keys never leave device, no third-party access, true air-gapped storage. Hot wallet: user controls keys but keys in software, app developer trust, online environment. Both offer non-custodial option; Ledger provides maximum self-custody.
Asset Protection
Asset Protection for Ledger vs hot wallets examine hardware vs software wallet safeguards through cold storage vs hot storage asset methodology including bitcoin & ethereum cold storage implementation, hot wallet multisig options availability, and token storage security assessment for crypto wallet safety comparison holdings context.
Bitcoin and Ethereum Cold Storage
| Asset | Ledger Security | Hot Wallet Security |
|---|---|---|
| Bitcoin | Offline signing | Online environment |
| Ethereum | Secure element | Software storage |
| Staking | Ledger Live integration | Direct protocol access |
| DeFi | WalletConnect secure | Native integration |
| Layer 2 | Supported | Native support |
Bitcoin & ethereum cold storage establishes Ledger vs hot wallets primary asset protection. Hot wallet multisig options include Gnosis Safe multisig, Argent social recovery, multiple signature requirement, threshold signing schemes, smart contract wallets. Token storage security: Ledger supports 5500+ tokens, all cold stored; hot wallets variable support, online storage; both ERC20 compatible and NFT support available.
Attack Scenarios
Attack Scenarios for Ledger vs hot wallets examine hardware vs software wallet threat exposure through cold storage vs hot storage attack analysis including ledger resistant to malware evaluation, hot wallets risk analysis assessment, and historical security incidents review.
Ledger Resistant to Malware
| Attack Type | Ledger Exposure | Hot Wallet Exposure |
|---|---|---|
| Keylogger | Immune | Vulnerable |
| Clipboard hijack | Protected | Vulnerable |
| Screen capture | Protected | Vulnerable |
| RAT access | Limited | Full access |
| Browser exploit | Immune | Vulnerable |
Hot wallets risk analysis: constant attack surface, browser extension risks, mobile app vulnerabilities, phishing susceptibility, malware infection vectors, social engineering targets, supply chain attack exposure. Historical security incidents: hot wallet phishing billions lost, exchange hot wallets major breaches, browser extension hacks millions stolen; Ledger device hacks zero keys compromised; hardware wallets safest track record.
For usability comparison, see our Performance & Convenience. For cost analysis, visit Cost vs Benefit Analysis.
Frequently Asked Questions
Yes. Ledger stores keys offline in secure element. Hot wallets expose keys to internet-connected environment with continuous attack surface.
Yes. Internet-connected wallets vulnerable to malware, phishing, and remote exploits. Hardware wallets require physical device presence.
Key storage location. Ledger stores keys offline in certified secure element. Hot wallets store keys on internet-connected devices.
Acceptable for small, frequently traded amounts. Hardware wallet recommended for significant holdings requiring maximum security.
No keys compromised from Ledger devices. 2020 customer database breach (emails, not funds). Device security remains uncompromised.
Keyloggers, clipboard hijacking, malware, phishing, remote access, and browser exploits. Transaction verification on device prevents address substitution.
Yes. Hot wallet for daily transactions and small amounts. Cold wallet for long-term storage and significant holdings.